Release Notes
June 2019 - Release 2
What's New
In our second June release, we are introducing the beta of our support for macOS. In addition to Android and iOS, KACE Cloud MDM will now offer device management for macOS devices. The new feature lets administrators streamline configuration of corporate settings including apps, VPN, and Wi-Fi, as well as simplify device enrollment with the Apple Device Enrollment Program (DEP).
If you are an existing customer and would like to access the macOS beta, please visit How to join the KACE Cloud MDM beta program where you can review details, read and accept the beta agreement, and finalize your participation.
New Feature: macOS beta
Functional details of the macOS beta release include:
Enrolling Devices:
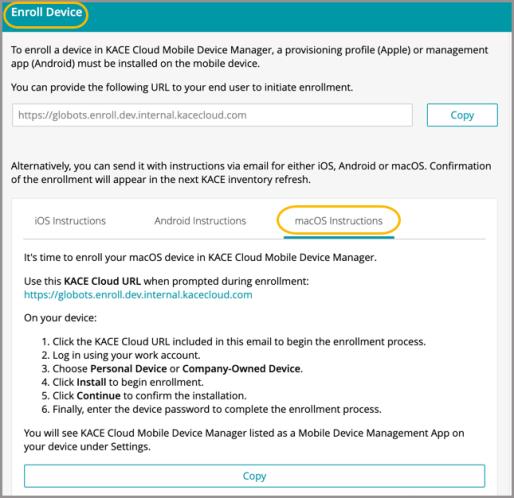
macOS Enrollment - macOS device enrollment follows the same process as enrolling an iOS device. First, a provisioning profile must be installed on the mobile device, then the admin provides an enrollment URL to the device user to initiate enrollment. Note that accounts are not supported for macOS, and passcode rules are not currently supported, but will be added as a feature in an upcoming release.
Apple Device Enrollment Program - The Apple Device Enrollment Program (DEP) is also available to admins enrolling macOS devices. Apple DEP lets admins create an automated device enrollment process for their end users on macOS devices. Set up automated enrollment using Apple DEP.
App Deployment:
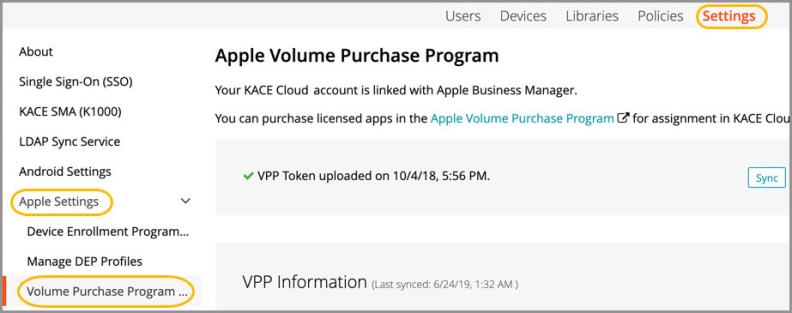
VPP Apps - To deploy apps from the Mac App Store to an enrolled Mac, apps must first be purchased or selected through the Apple Volume Purchase Program. Once purchased and synced, apps will appear in the Apps section of the Library. Learn more about VPP and App License Management.
Custom Apps - Custom apps must be installed using signed distribution packages. This requires two commands to be run on a macOS device with an Apple code signing certificate. Learn more in macOS - App Management.
Device Configurations:
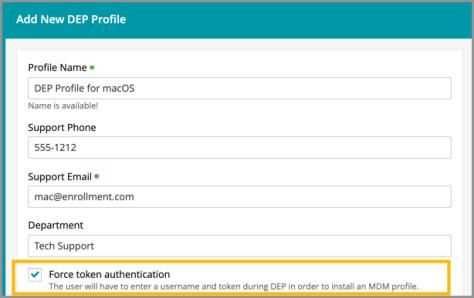
macOS-specific Settings - When creating a DEP profile, an admin can choose macOS-specific settings for devices. macOS options include the ability to force token authentication, set supervision in the form of local user accounts, and set disk access options.
Force Token Authentication - When configuring a device with a DEP profile on a Mac-enabled tenant, an admin can enable 'force token authentication'. This setting forces a user to enter their username and a deployment token to enroll their device. This restriction helps prevent unauthorized access to sensitive customer information like VPNs, certificates, and custom applications.
Passcode Policy for macOS - Passcode rules are not currently supported, but will be added as a feature in an upcoming release.
macOS-specific Commands
macOS Profiles - To create a custom Apple Profile for a macOS device, an admin can use the macOS Server utility. Custom profiles can then be applied to different devices that are managed in KACE Cloud MDM.
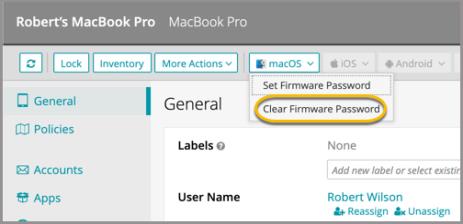
Set/Clear Firmware Password - In addition to protecting the data on macOS devices with a user account password, admins can set a firmware password to prevent unauthorized start-up of a device. If a device comes into KACE Cloud MDM with a firmware password already set, an admin will need to clear that password and reset it.
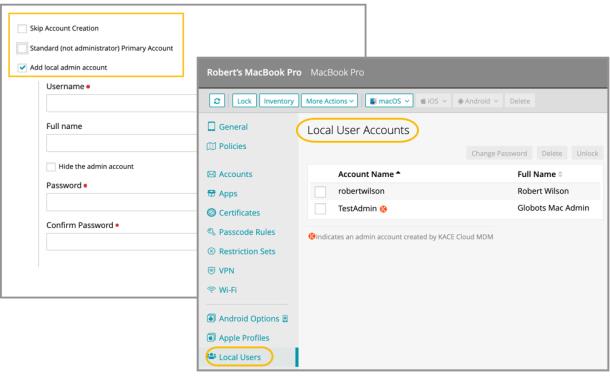
Local User Accounts - During account setup, an admin can choose one or more account restrictions to assign admin-level control of the device. Different local admins can be assigned to certain devices using different profiles.
Known Issues
Role Management and SSO Configuration
If user role assignment is set to Automatic during SSO Configuration, a manual attempt to update an individual user's role via the Users > Edit User path may appear possible, but will be overwritten by the original SSO Configuration. To resolve, the configuration setting can be changed to Manual, which will then enable editing of individual user roles.
Android-Specific Considerations
Device Owner Setup
When using the Device Owner enrollment flow (afw#kace), the enrollment flow may not complete if the Google Play services on the factory default image of the device are out of date. This a known issue with the Android operating system, caused by the enrollment process timing out before the update of the Play services on the device can complete. You will know that this situation occurred if you are never asked for your subdomain name during the enrollment process. If you end up back at the device home screen, locate and launch the KACE Cloud MDM agent app on the device and click the 'Enroll Device' button to complete the setup process.
Gmail App
Android devices require the Gmail app to be installed in order to use the email account configurations.
Set and Clear Passcode Commands
The set and clear passcode functions are different in Android 7.0 and later. On versions prior to 7.0, an administrator could set or clear the passcode as desired. On Android 7.0 and later, the passcode can only be set on devices that do not already have a passcode set, and passcodes cannot be cleared. The user interface does not currently warn users who are attempting to set or clear a passcode on Android 7.0 and later, but an error message will appear. Note that attempting to clear a passcode will also fail if there is a policy in place that requires use of a passcode to do so.
iOS-Specific Considerations
Factory Reset - Apple iOS iCloud Account Lock
When resetting an Apple iOS device back to factory defaults, the device will remain locked to the associated iCloud account. To prevent this from happening, before resetting the device, manually turn off the 'Find my phone' feature on the iPhone.
Additional Resources
Getting Started with KACE Cloud MDM
© 2019 Quest Software Inc.
ALL RIGHTS RESERVED.
This guide contains proprietary information protected by copyright. The software described in this guide is furnished under a software license or nondisclosure agreement. This software may be used or copied only in accordance with the terms of the applicable agreement. No part of this guide may be reproduced or transmitted in any form or by any means, electronic or mechanical, including photocopying and recording for any purpose other than the purchaser’s personal use without the written permission of Quest Software Inc.
The information in this document is provided in connection with Quest Software products. No license, express or implied, by estoppel or otherwise, to any intellectual property right is granted by this document or in connection with the sale of Quest Software products. EXCEPT AS SET FORTH IN THE TERMS AND CONDITIONS AS SPECIFIED IN THE LICENSE AGREEMENT FOR THIS PRODUCT, QUEST SOFTWARE ASSUMES NO LIABILITY WHATSOEVER AND DISCLAIMS ANY EXPRESS, IMPLIED OR STATUTORY WARRANTY RELATING TO ITS PRODUCTS INCLUDING, BUT NOT LIMITED TO, THE IMPLIED WARRANTY OF MERCHANTABILITY, FITNESS FOR A PARTICULAR PURPOSE, OR NON-INFRINGEMENT. IN NO EVENT SHALL QUEST SOFTWARE BE LIABLE FOR ANY DIRECT, INDIRECT, CONSEQUENTIAL, PUNITIVE, SPECIAL OR INCIDENTAL DAMAGES (INCLUDING, WITHOUT LIMITATION, DAMAGES FOR LOSS OF PROFITS, BUSINESS INTERRUPTION OR LOSS OF INFORMATION) ARISING OUT OF THE USE OR INABILITY TO USE THIS DOCUMENT, EVEN IF QUEST SOFTWARE HAS BEEN ADVISED OF THE POSSIBILITY OF SUCH DAMAGES. Quest Software makes no representations or warranties with respect to the accuracy or completeness of the contents of this document and reserves the right to make changes to specifications and product descriptions at any time without notice. Quest Software does not make any commitment to update the information contained in this document.
If you have any questions regarding your potential use of this material, contact:
Quest Software Inc.
Attn: LEGAL Dept.
4 Polaris Way
Aliso Viejo, CA 92656
Refer to our website (www.quest.com) for regional and international office information.
Patents
Quest Software is proud of our advanced technology. Patents and pending patents may apply to this product. For the most current information about applicable patents for this product, please visit our website at www.quest.com/legal.
Trademarks
Quest and the Quest logo are trademarks and registered trademarks of Quest Software Inc. in the U.S.A. and other countries. For a complete list of Quest Software trademarks, please visit our website at www.quest.com/legal. All other trademarks, servicemarks, registered trademarks, and registered servicemarks are the property of their respective owners.